
As a computer user, of course we all want a good computer performance, fast response, smooth data access without having to wait a long time and so on. There is therefore good that we know what the cause or an effect with a slow computer. The following brief review 9 of the most frequent causes slow computer performance plus tips or solution.
1. Malware (virus, worm, trojan, dsb )

When computers are exposed to malware (viruses, worms, trojans, and the like), it's almost certain that okmputer performance will be slow. The virus will often use the computer's resources either RAM or CPU, as well as continuously monitoring computer activity. It is certainly very influential on the performance of other applications.
The solution to prevent this for users of Windows is to install antivirus and not just stop there, but regular antivirus updates. Schedule at least once a week if the computer is not online.
2. Spyware, Adware and The Like

If we often use the computer to the internet for, if not careful there is a possibility the computer may be infected with spyware. The effect may not be so great with the computer's performance, but it could have an effect on Internet access, and various things that disturb the comfort of surf and worse, important data (user, password, account, etc.) we can know by the creator of this spyware.
Solutions can install Anti-spyware is also constantly updated, just need to be sorted out which ones are not much use of my resources (resources) of our computer, because it is not uncommon Antispyware uses the CPU and Memory that is large enough. If antivirus is included, we do not need to add. Or use a portable version, and regularly scan for spyware only.
3. The number of applications running in the background

The more our computers with software, usually the more slow computer performance, although there is a relatively small effect and there are great. It is important to note when installing software, check whether an application is always running behind. This can be in the know with programs like Autoruns.
The solution in this case is important to use the software only, select a software if there is some similar software or have similar features and if there is a portable version of it then it could be an alternative. To reduce the program running in the background, use Autoruns, and disable unnecessary background applications. To to see whether the application is installed to run the program in the back, install software such as WinPatrol.
4. Hard disk (HDD) that have been age

When computers are still using the hard disk that is long enough (old), may be more than 5 years, then get progressively slower computer performance. To check, we can use free software HDD Tune and the like (read the article: Check the condition of your Computer Hard Disk). Normal SATA HDD usually average read access (read) about 70-90 MB / s. If for example the average HDD access below 50 MB / s then the performance will usually feels slow.
Solution when the hard drive is very slow, may be tried with full format (beware, data backup first). Although the old hard drive to it typically will not help much, so it is best to replace a new hard drive, and if you still want to use the old hard drive, use as a secondary hard drive only.
5. RAM / Memory mediocre

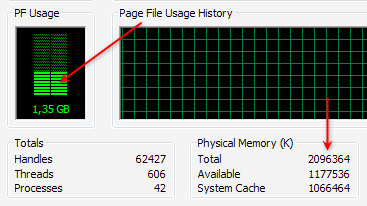
Many of the least amount of RAM / memory that we use can not be made a standard equal to one computer to another computer or even the operating system. Although when it will install Windows, there is a minimum specification of RAM, but the type of application that we use must also be taken into account. To check, just open the
Task Manager and in the
Performance check the PF Usage and also showing the total Physical Memory Physical Memory (RAM) and the remaining available (Available).
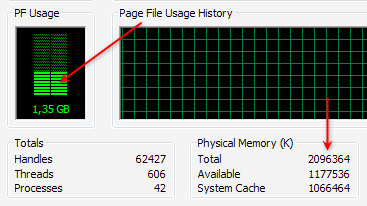
If we are not running any applications, but the rest of RAM is more than half, usually the computer's performance will be slow, then it should be checked any application that uses lots of memory (RAM), generally can be checked at the Process , Mem Usage column . If indeed we are barely adequate RAM (eg Windows XP with 512 MB of RAM or less, windows 7 with 1 GB of RAM), then the cheapest solution is to reduce the applications that consume a lot of memory. The best solution is to upgrade memory (RAM) (read: Know what RAM).
6. Conflicts applications or programs installed

Not infrequently two applications in the same category could result in conflict, further slowing computer performance. Signs of conflict forged the troubled computer after you install the software, whereas previously there was no problem. What often happens is usually in the category of conflict security software, such as antivirus.
For example we use 2 antivirus or more. Although some antivirus can run concurrently, but still not recommended, except for expert users or for trial. Not to mention when it still had to install other security software.
If there is an alternative variety of similar software, then if possible choose one that can represent, and superior in performance and results. Especially for the many types of software to access the resources or the operating system.
7. Selection Software inappropriate

Not a few people just went along with (trend) in the use of software, but there is actually a desirable feature in other software that is small and free. If we are indeed minimal computer specs or we want to work quickly, then choose the right software. Software with a large size is not always better and more appropriate for each of us. Here are some examples:
When we just want to burn data to CD / DVDs, exact solutions can use ImgBurn software that measures just about 5 MB or other free burning software that is relatively smaller than installing Nero Multimedia Suite which is about 354 MB.
When we work with compressed data (zip, rar), free software like 7zip that measures just about 1 MB should suffice, rather than install Winzip 15 measuring nearly 13 MB and is also not free (free compression software, etc.)
If using Photoshop 7 or CS1 / 2 is sufficient for the needs of graphics, then install Photoshop CS5 need difikir repeated, because the required specification is quite high, so it can work more slowly.
8. The amount of software installed

Although the software is installed is not running behind, but almost every software always adds an entry (data) to the registry, so that more and more software is installed is the size of the registry (windows) will also be greater. Because the registry will be accessible both when the computer is running and is already running, the size also affects the speed / response time was.
The solution is to use software that's required course, Uninstall software that is not important and use the uninstaller like Revo Uninstaller to make the process more thoroughly uninstallasi. To clean the software has been uninstalled on, can also use a variety of free Utilities.
9. Effects of excessive use of Windows

The use of Windows berlebihWindows Securities Xp, Vista and Windows 7 provides the option to use a display with various effects. If your computer has good specs, of the various effects is not a problem, but if you want faster performance, the effects of windows can be deactivated.
For example Windows XP, right-click My Computer, select the Advanced tab and click the Performance setting. We also put through the system tweaked to get the settings right and quickly, using software such as X-Setup Pro.

Actually, in addition to the above 9 things are still many other reasons, such as various service windows that are running are actually not necessary, selection and arrangement of hardware that is not optimal, the primary disk space (for example, drive C:) which limits or on the verge of running out, and others (ebsoft)
















 Although the software is installed is not running behind, but almost every software always adds an entry (data) to the registry, so that more and more software is installed is the size of the registry (windows) will also be greater. Because the registry will be accessible both when the computer is running and is already running, the size also affects the speed / response time was.
Although the software is installed is not running behind, but almost every software always adds an entry (data) to the registry, so that more and more software is installed is the size of the registry (windows) will also be greater. Because the registry will be accessible both when the computer is running and is already running, the size also affects the speed / response time was.







